Re-Usable Designs
Reusable design components form the architectural backbone of scalable conversational skills. These modular blocks handle everyday interactions—like authentication—and can be deployed across various flows with minimal modification. Think of them as "copy-paste" blueprints that accelerate design while maintaining a consistent user experience.
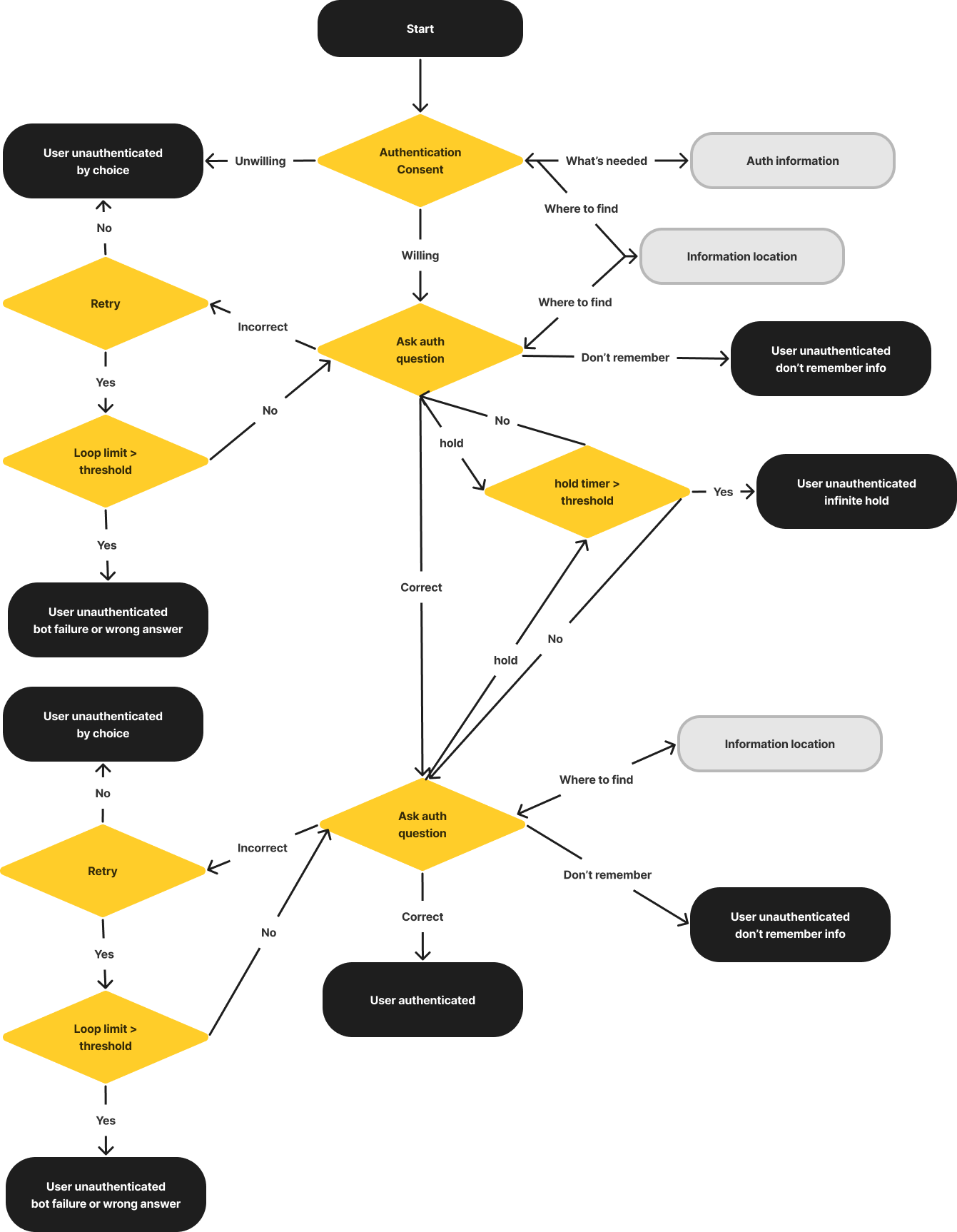
Level 1 Authentication
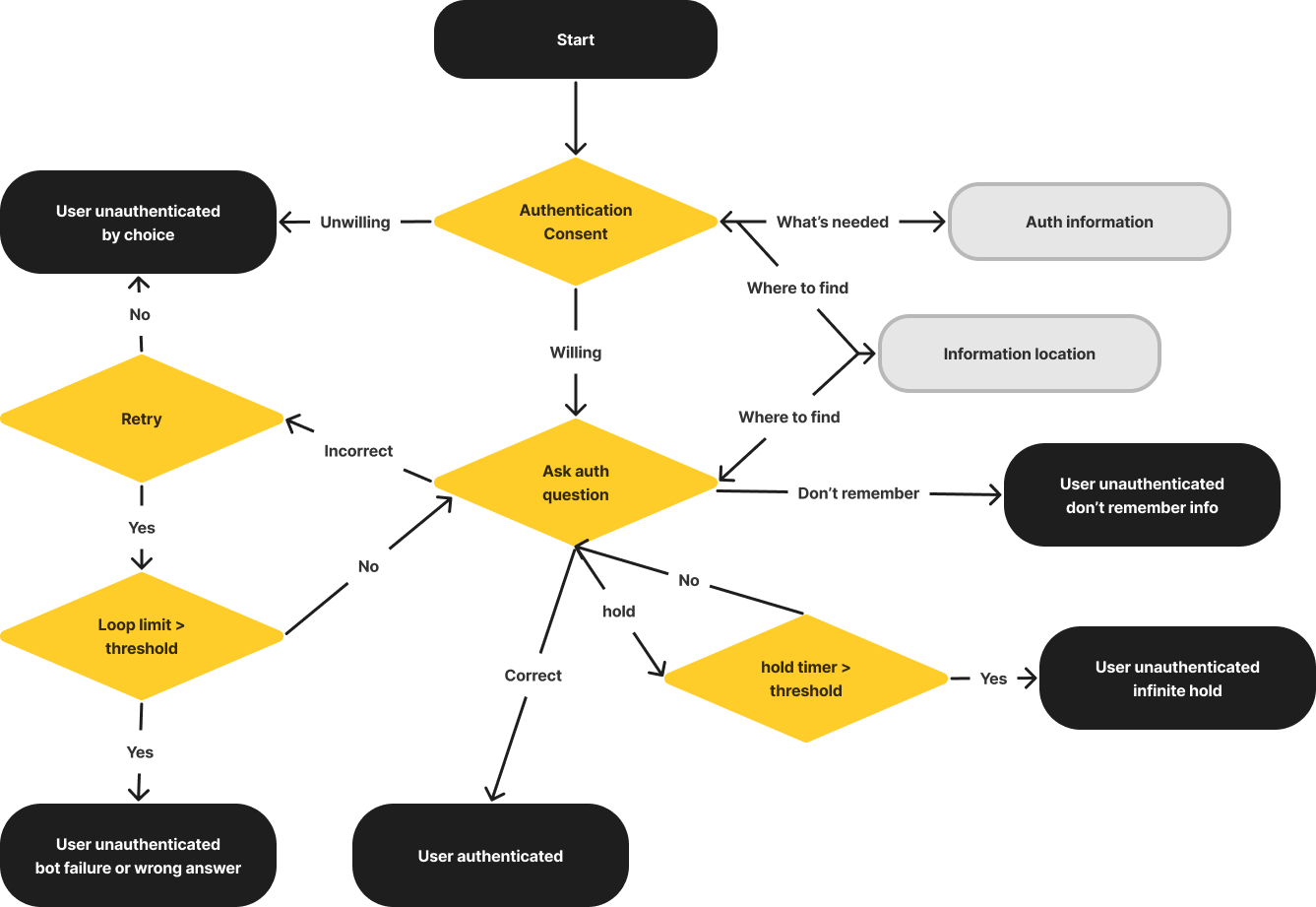
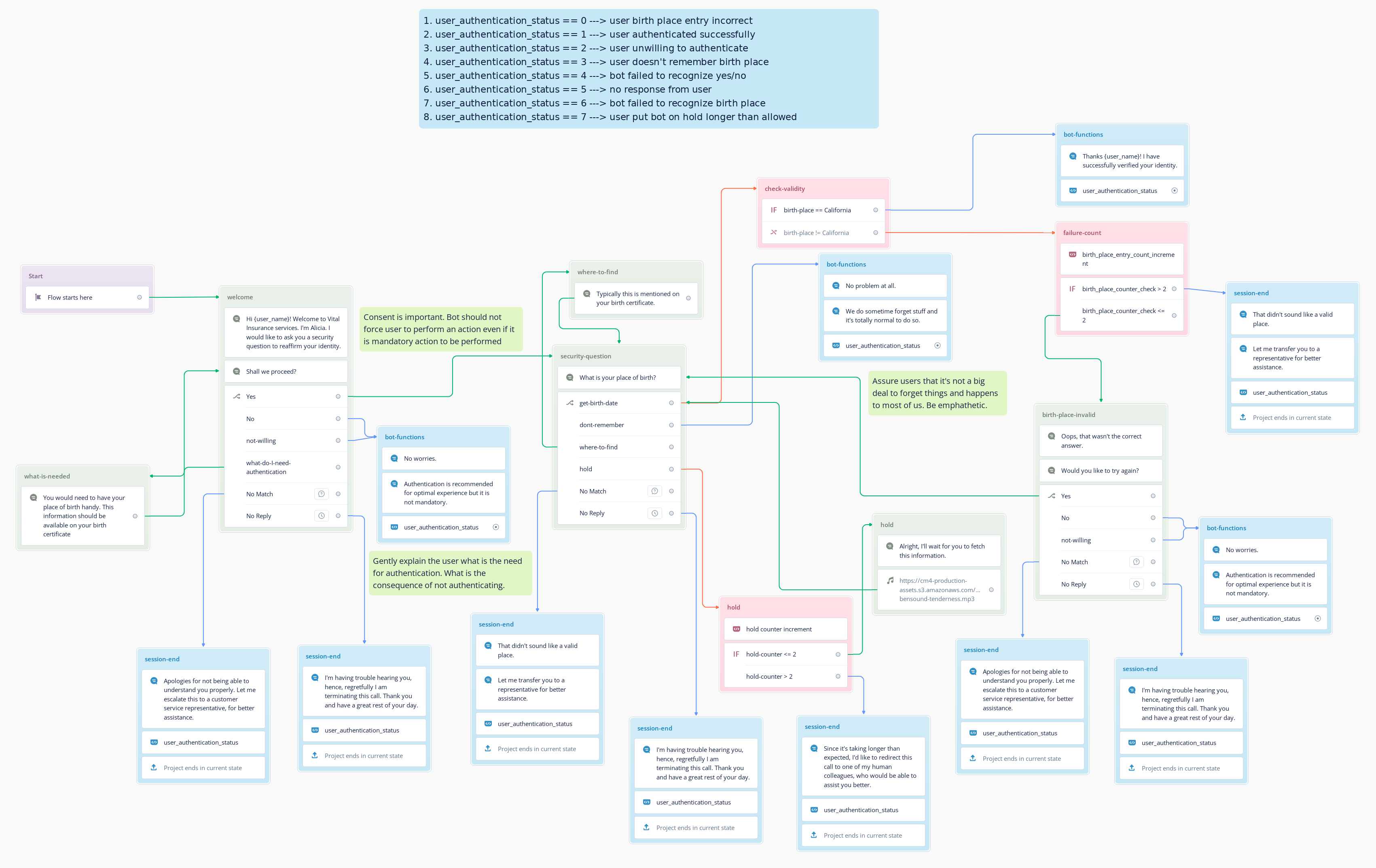
A streamlined, single-factor authentication (1FA) flow where the bot verifies user identity via a single security question.
Below is the architectural blueprint for capturing this single data point efficiently.
High-level design
Example implementation: Birthplace capture
Validating user identity by asking for their registered place of birth.
Core Design Principles:
- Consent First - Never impose security checks. Always request explicit user consent before initiating the authentication flow.
- The Gentle Nudge - If consent is denied, apply a soft nudge explaining the benefits of authentication, or gracefully fall back to limited functionality.
- Edge-Case Resilience - Proactively design for "not-so-happy" paths: clarify what is needed, explain where to find it, accommodate "hold" requests, and reassure users if they simply forget.
- Consistent Persona - Maintain the bot's character (e.g., a helpful service desk agent) throughout the security check to keep the experience human-centric.
- Exit Point Mapping - Log precise exit statuses for every drop-off point. This provides instant visibility into conversation outcomes without requiring deep data mining.
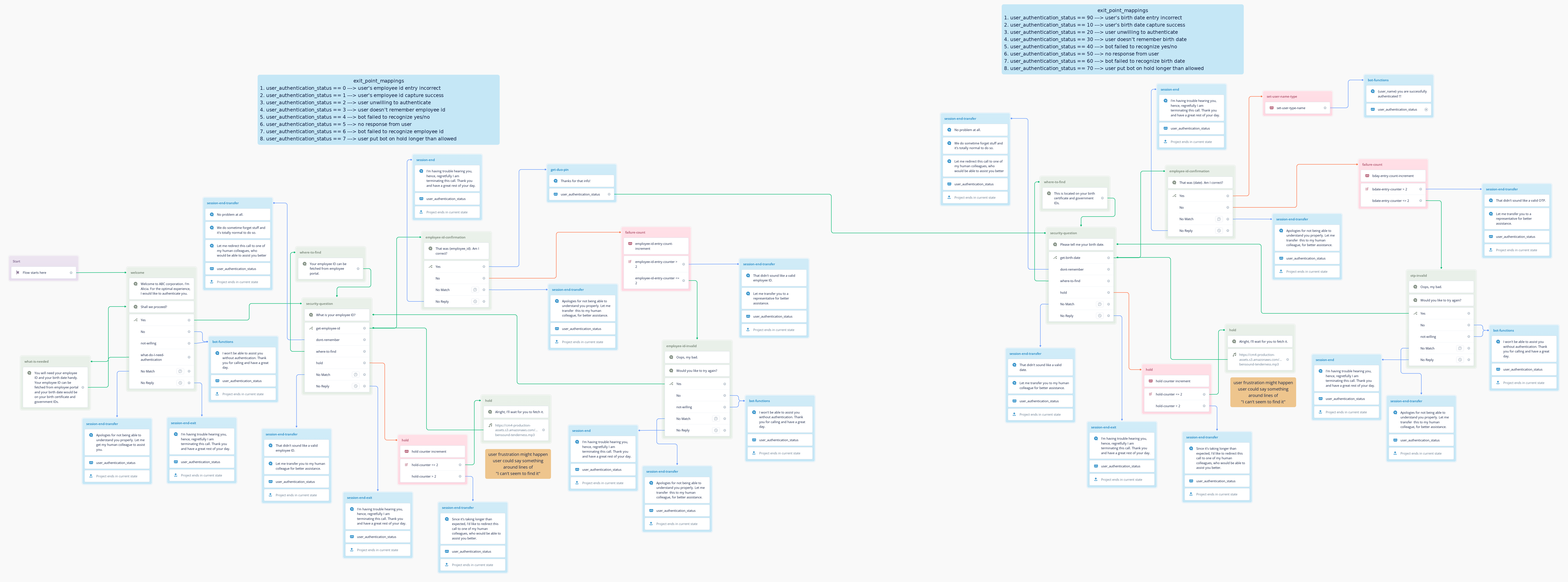
Level 2 Authentication (Non-OTP)
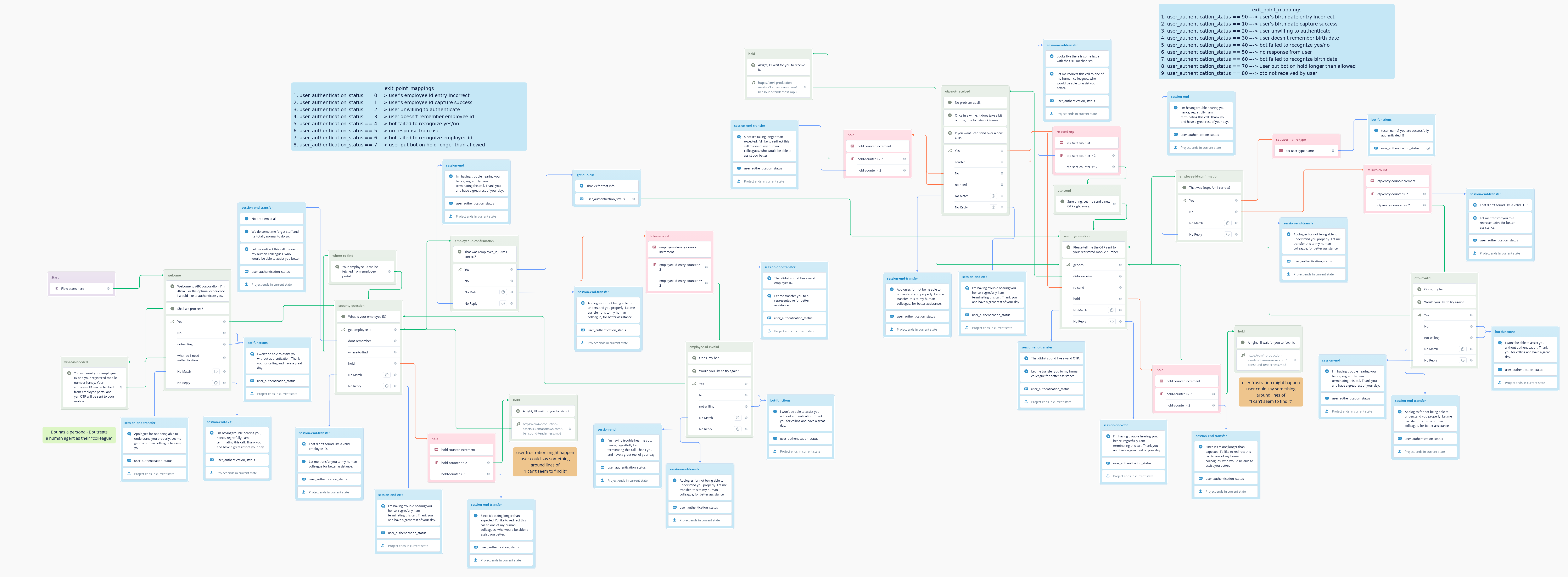
A two-factor authentication (2FA) flow relying on two distinct pieces of static user knowledge. This structure applies when dynamic passcodes are unavailable.
Below is the blueprint for chaining two verification steps smoothly.
High-level design
Example implementation: Employee ID & Birth Date
Validating internal users by capturing two distinct data points in sequence.
Core Design Principles:
- Consent First - Establish trust by confirming the user is ready to provide multiple pieces of personal data.
- The Gentle Nudge - Counter hesitation by explaining why these specific details are required for access.
- Edge-Case Resilience - Handle compounding errors gracefully. Guide the user on where to locate their ID and reassure them if they struggle with the format.
- Consistent Persona - Keep the tone conversational, avoiding overly robotic or interrogative prompts.
- Exit Point Mapping - Track exactly which of the two questions caused the drop-off to identify points of highest friction.
Level 2 Authentication (OTP Based)
A dynamic Multi-Factor Authentication (MFA) flow leveraging one piece of static knowledge and a real-time, system-generated One-Time Password (OTP).
Below is the blueprint for handling the unpredictable variables of network latency and SMS delivery.
High-level design
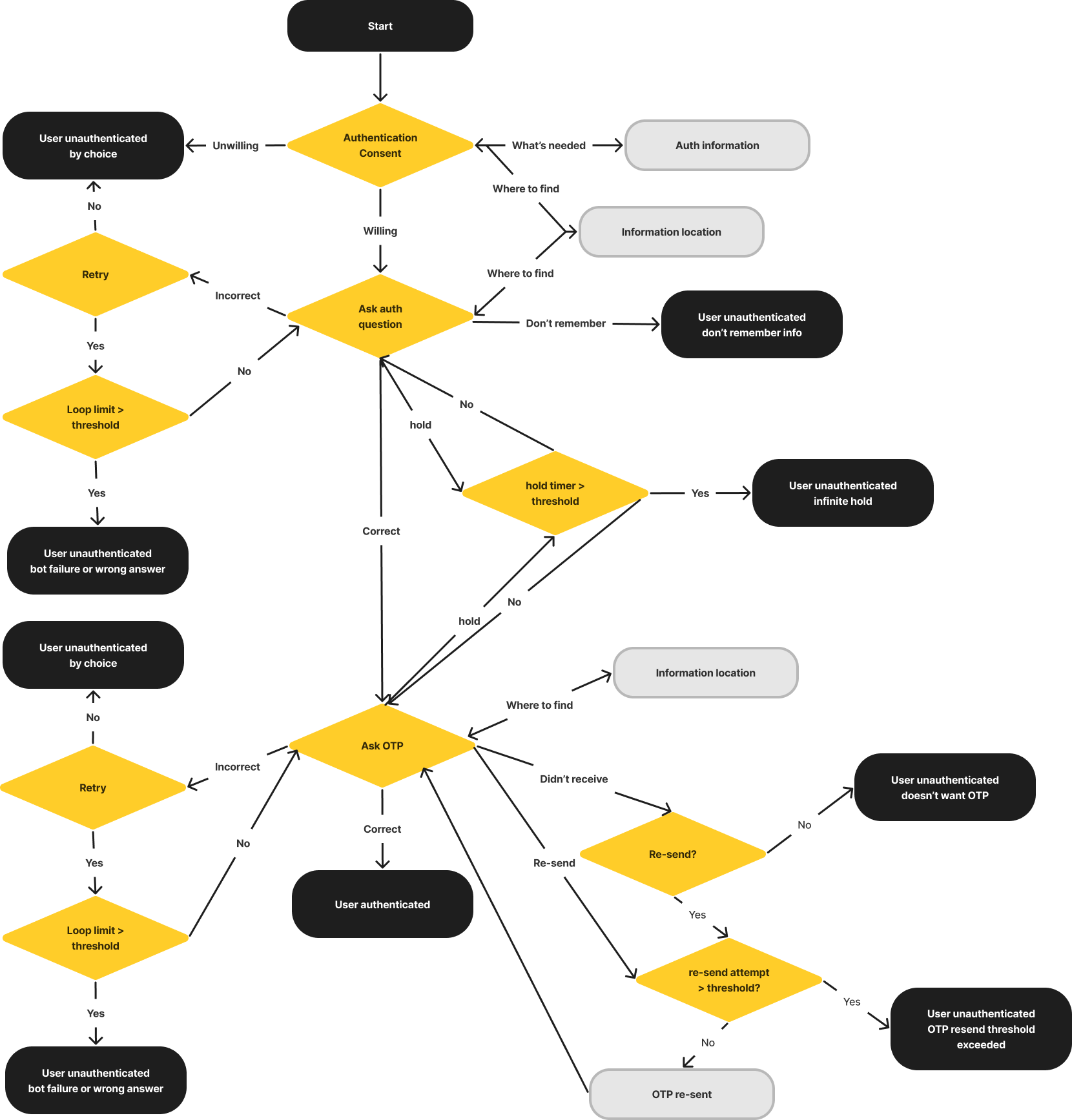
Example implementation: Employee ID & OTP
Verifying the user's ID before dispatching a dynamic passcode to their registered mobile device.
Core Design Principles:
- Consent First - Ensure the user is ready to receive and read a message before triggering the API call.
- The Gentle Nudge - Offer alternative, limited-access paths if the user does not have their phone handy.
- OTP Friction Handling - Anticipate delivery delays. Reassure users that network latency is normal before blindly resending the code, as every SMS transaction carries a financial cost.
- Retry Logic - Provide a clear, controlled mechanism to request a new OTP if the original expires or fails to arrive.
- Consistent Persona - Project competence and patience while the user navigates between the call and their messaging app.
- Exit Point Mapping - Clearly distinguish between users who abandoned the flow due to an incorrect ID versus those who failed at the OTP step.